The Story of Cryptography
Part 1: Historical Cryptography

Cryptography is the science of secrets. Literally meaning 'hidden writing,' cryptography is a method of hiding and protecting information by using a code, or cipher, only decipherable by its intended recipient. Today, modern cryptography is essential to the secure Internet, corporate cybersecurity, and blockchain technology. However, the earliest use of ciphers dates back to around 100 BC.
In this three-part series, we will explore the history of cryptography before the 20th century, in the 20th century, and in the modern day.
Historical Cryptography
Caesar Box
The "Caesar Box," or "Caesar Cipher," is one of the earliest known ciphers. Developed around 100 BC, it was used by Julius Caesar to send secret messages to his generals in the field. In the event that one of his messages got intercepted, his opponent could not read them. This obviously gave him a great strategic advantage. So, what was the code?
Caesar shifted each letter of his message three letters to the right to produce what could be called the ciphertext. The ciphertext is what the enemy would see instead of the true message. So, for example, if Caesar’s messages were written in the English alphabet, each letter “A” in the message would become a "D," the "B’s" would become "E’s," and the "X's" become "A’s." This type of cipher is appropriately called a “shift cipher.”
Caesar’s magic number was three, however, a modern day use of the Caesar Cipher is a code called "ROT13." ROT13, short for "rotate by 13 places," shifts each letter of the English alphabet 13 spaces. It is often used in online forums to hide information such as movie and tv show spoilers, solutions to puzzles or games, or offensive material. The code is easily crackable, however, it hides the information from the quick glance.
GhostVolt Solo
Rock Solid File Encryption for Everyone
Protect against data theft and easily lock any file with automated encryption, organise with file tagging and securely share your files with anyone.
Cryptanalysis: Breaking a Caesar Box
The hardest part of breaking a Caesar Box is figuring out the language of the message that it encodes. Once the code cracker figures this out, two scenarios are considered. Either the “attacker” utilizes a technique such as frequency analysis, or they use what is referred to as a brute force attack.
In the first instance, the attacker knows that certain letters are used more frequently than others. For example, A,E,O, and T are the most commonly used letters, while Q, X, and Z are the least. The relative frequencies of each letter in the English language are shown in the graph below.
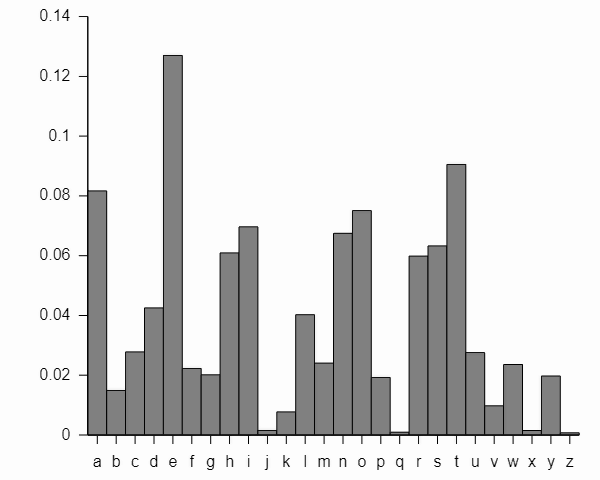
If using a simple substitution cipher such as frequency analysis does not crack the code, an attacker could perform a brute force attack. This kind of attack entails testing each possible shift on a small snippet of the message. So, if the message is written in English, this would require a maximum of 26 tests since there are 26 letters in the English alphabet. While this is not a particularly sophisticated attack, it is effective.
The Vigenère Cipher
The Vigenère Cipher, created in the 16th century, uses an element not found in a Caesar Cipher: a secret key. The creator of the code picks any word or combination of letters at random to be the key, for example, “DOG.” The keyword chosen will then be matched to the plaintext message that you want to encrypt, for example, "ATTACK." You can see that the keyword "dog" is shorter than the word “attack" by three letters. In this case, repeat your key until it matches the number of letters in your plaintext message. In this case, you would then have "DOGDOG."
Now, you will be able to create the ciphertext. To do this, you will need to use the chart below.
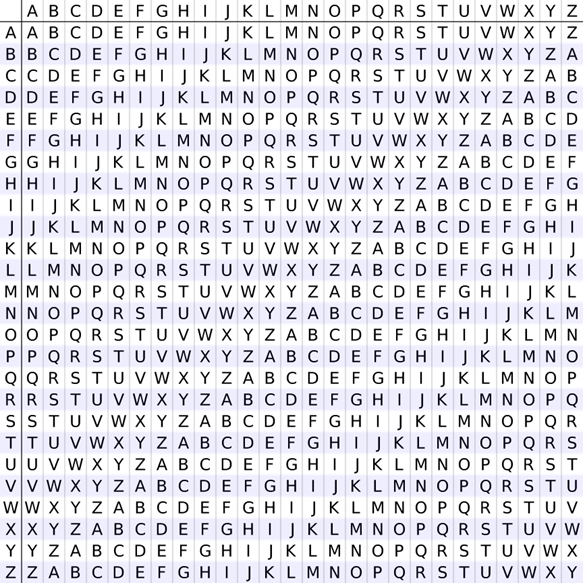
The columns are the letters of the secret key, while the rows are the letters of the plaintext message. So for our example, the first letter of our key is “D,” while the first letter of our plaintext word is “A.” So, find where they intersect on the chart, and you will find the first letter of our ciphertext, which is “D.” Next, the second letters of our key and plaintext words are “O” and “T” respectively. They intersect at “H.” You would continue this until you complete all six letters.
Plaintext Message: ATTACK
Key: DOGDOG
Ciphertext: DHZDQQ
Cryptanalysis: Cracking a Vigenère Cipher
Because of the use of a key, the Vigenère Cipher cannot initially be cracked by using a simple frequency analysis like you could do with a Caesar Cipher. Though, the main weakness of a Vigenère Cipher is the repeating of the key. So, in our example, “dog” was repeated twice in order to match the number of letters in the word “attack.” If an attacker guesses the key’s length, it becomes much easier to crack. The ciphertext is then treated like a series of small Caesar Ciphers, and a method such as frequency analysis could then be performed to crack the code.
But how can an attacker guess the length of the key? There are actually two methods: the Kasiski examination and the Friedman test. If the attacker notices that there are repeated segments of text in the ciphertext, a Kasiski examination would be effective in cracking the code. The attacker would count the distance of letters between repeated text to get a good idea of how long the key is. The Friedman test takes an algebraic approach utilizing a formula to measure the unevenness of the cipher letter frequencies to break the cipher. The longer the text, the more accurate this technique is.
Coming Up: 20th Century Ciphers
The Caesar Box and the Vigenère Cipher are two of the earliest known ciphers. They pioneered the use of encryption to protect sensitive communications data and the use of a secret key in encryption. In the next post in this series, we will move forward to the 20th century. We will see how cryptography evolved when driven by both military interests and organizations protecting their intellectual property.
GhostVolt Solo
Rock Solid File Encryption for Everyone
• Protect against data theft
• Easily lock any file
• Automated encryption
• Secure file sharing
• File tagging
• Super easy to use
Guest author Howard Poston is a cybersecurity and blockchain security consultant and trainer. You can reach Howard at howard.poston@gmail.com