Advantages of Using Encryption
When using the Internet, most people know to use encryption of data in transit. This is the big difference between HTTP and HTTPS traffic (i.e. whether or not the lock icon shows up in the address bar). Using HTTPS helps to ensure that you’re connected to the right website and that no one can eavesdrop on your connection, which may include personal data like credit card information, your Netflix queue, etc.
However, your personal data isn’t only at risk when it’s traveling over the Internet. Despite your best efforts, there is a chance that your computer will be infected with malware that your antivirus doesn’t catch. If this is the case, the malware may start looking for sensitive data on your computer and send it to the cybercriminal running the malware.
This is where file encryption comes in. Instead of just encrypting data in transit, file encryption ensures that data is stored encrypted on your computer. This means that an attacker or malware with access to your computer can’t read your sensitive data unless they also know your password.

Encryption protects your privacy
The most common argument against implementing good cybersecurity practices is “I don’t have any data worth stealing”. However, this statement is incorrect, and cybercriminals commonly target individuals to steal personal data.
When thinking about your personal data, you might focus on credit card and banking information, which is primarily entered into the browser and not stored on the machine. A great deal of personal data can be extracted from files that you may store on your computer without thinking twice about them. Some examples of these files include:
- Tax Return Documents:
Most tax preparation software provides an option to store a copy of the return on your computer. A full tax return provides an attacker with all of the information that they require to perform identity theft. Similarly, W2s, 1099s, and other common forms can contain sensitive data. - Family Photos:
By default, many cameras and smartphones will embed location information in photos, which is why your computer can tell where and when the photo is taken. A picture of a backyard barbecue can reveal a home address, or a birthday photo reveals someone’s name and date of birth. - Application Forms:
Applications for a loan, rental, etc. often contain sensitive information like a social security number (SSN). This information can be used in identity theft scams. - Travel Plans:
When booking a vacation, you may store a copy of the booking information on a computer. These confirmations can include financial information, information about your travel plans, and provide a would-be burglar with a list of dates when a house will be empty.
Product plug alert!
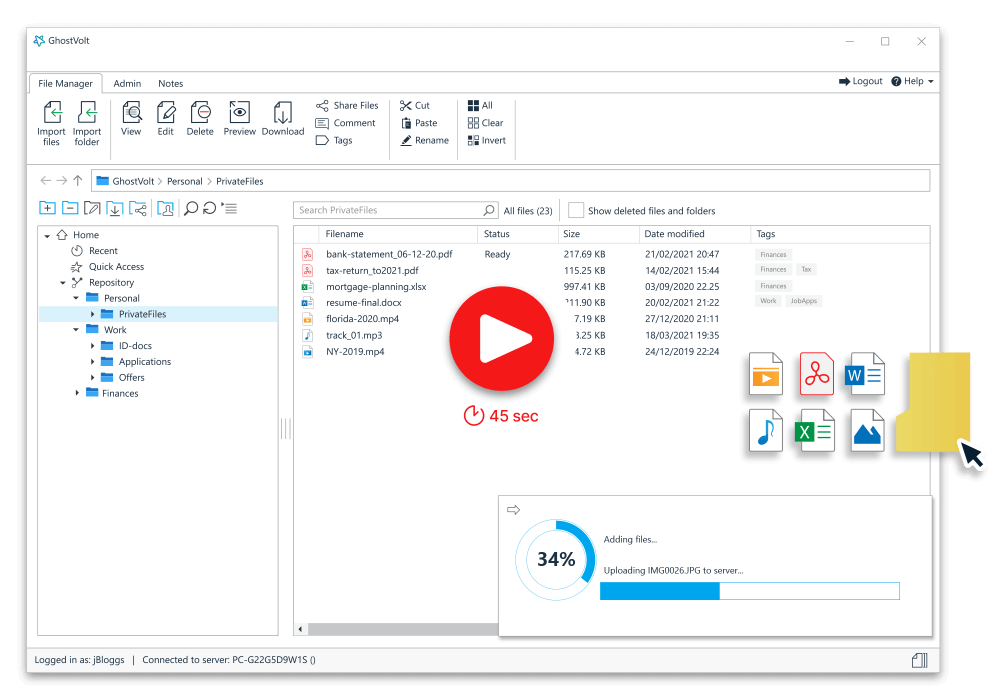
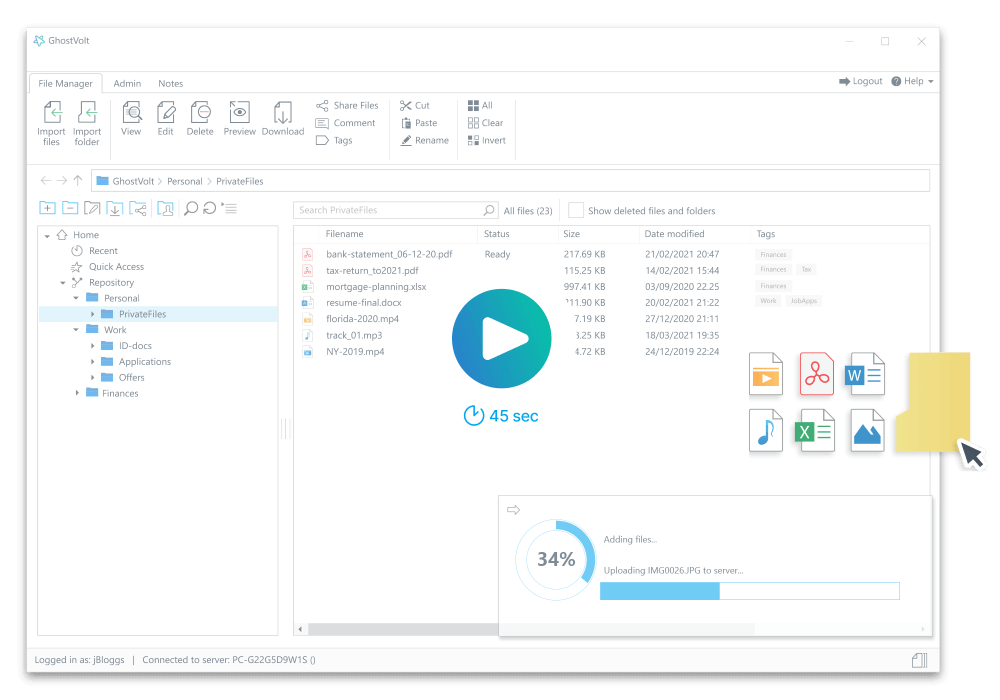
Simply add your files and folders to GhostVolt and they're automatically encrypted. Once encrypted, only you can access your files and folders, everyone else is denied access including your family, employer, or anyone else who can access your computer.

Encryption Protects you and your Identity
At this point we all know what ransomware is and the effect it can have on you or your business (if you don’t know, head over to your favourite news channel and peruse the technology section). But what is not so well known is the latest “trendy” way in which cybercriminals are using ransomware to blackmail you into paying ransoms.
The latest trend in ransomware is to bypass the encryption of your files and instead, steal all your data which is then used to blackmail you into paying a ransom. If you do not pay-up, your data its leaked on the internet, used for identity theft or just sold to the highest bidder.
Encrypting your files is a critical part of your defense against cybercriminal attacks, including ransomware. When your files are encrypted, criminals cannot access your data. Instead, they can only see a scrambled nonsense (random letters, numbers and symbols) which is useless to them and therefore cannot be used for extortion or to hold you to ransom.
See how file encryption can help defend against Ransomware
Encryption protects your Cloud data
If you store your files and data on a Cloud backup platform such as OneDrive, Google Drive or DropBox, you may be concerned that your cloud provider has the master encryption key to access your data. Your fears are not unfounded. A quick search on DuckDuckGo and you’ll quickly find statements such as the following from DropBox:
(3) to enforce our Terms of Service and Acceptable Use Policy. Access to users’ file content is limited to a small number of people. We have strict policy and technical access controls that prohibit access to file content except in these rare circumstances.Link here
Rare circumstances? What does that even mean? I don’t know what constitutes a rare circumstance within DropBox, but what I can tell you is this, DropBox absolutely have the ability to read your files.
The best way to protect your Cloud data is encryption.
When you encrypt your cloud files and data, it stops your cloud provider from accessing them, even if they are forced by the government, the FBI or aliens. Why? Because your data is encrypted with your key, not theirs. So on those rare occasions
when they attempt to access your data, access is denied!
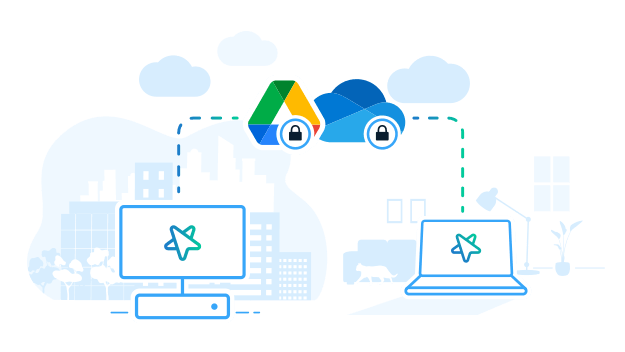
A word of caution: The App you choose to encrypt your cloud data must never encrypt or decrypt files within your cloud folder (e.g., your OneDrive folder on your computer), because if it does, your Cloud provider will sync your data before its encrypted.
Product plug alert!
GhostVolt performs all encryption and decryption in a location where your Cloud provider has zero access. This means only secure, encrypted files are saved to your cloud folder. No data leaks.

Encryption allows you to securly share your files
Sharing files online is more popular than ever. You do it on social media like Facebook, on messenger apps, forums, and cloud services. But what’s the risk? Only the people I’ve sent the file can see it, right? Wrong!
If your shared files are not encrypted, they’re accessible to everyone. Imagine the devastation of finding your private pictures or bank number scattered across the web…
The reason why it is important to encrypt files before sharing is simple – encrypting your files ensures your privacy. Someone unauthorized can’t open the files, meaning only you and your intended recipient gets access.
Product plug alert!
With GhostVolt, you can securely share your files with friends, family, customers or whoever. Share via the cloud, email, messenger or any other sharing App, it’s up to you.

Encryption protects Lost/Stolen Devices
Employees are increasingly using mobile devices for work. This trend has become more common in recent years, and the COVID-19 pandemic created an explosion in telework and the use of personal and mobile devices.
With the increased convenience of these mobile devices comes higher cybersecurity risk. A smartphone, tablet, or laptop is relatively easy to lose or have stolen in a public place. If this occurs, the thief may be able to read sensitive company data off of the device by scanning its hard drive.
File encryption protects against the threat of lost or stolen mobile devices. Each file on the machine is encrypted, and the encryption keys are stored protected by the user’s password. If an attacker doesn’t have access to this password, then they can’t read any useful data off of the stolen device.